
Recap: JT at MWC Barcelona 2026
Our teams were thrilled to be back at #MWC26 in Barcelona, capturing the energy, the innovation, and the big conversations ...

On-Demand Webinar | Secure, seamless, always on: How JT & Fortinet enable the modern workforce
Hybrid work has redefined how teams stay connected, productive, and secure. As users move between offices, homes, and cloud applications, ...

MWC 2026: AI, Security, Sustainability – A CFO’s Perspective
Author: Helene Narcy Group CFO and Director of Corporate Services, JT As CFO and Director of Corporate Services at JT, ...

Video: Transforming for You | Sara McCarthy, COO
We’re entering a new era of JT Enterprise — evolving from a traditional telco into a strategic partner that helps ...

Accelerate your move to hybrid cloud with government-backed funding
Author: Rose McCloskey Head of Jersey Enterprise, JT The Jersey Better Business Grant is reopening, giving Jersey-based businesses financial headroom ...

Beyond Networks: JT’s Vision for a Connected World
Author: James Solomon Head of Enterprise Product & MSP, JT Strong digital foundations are more important than ever. Businesses in ...

The evolving role of the CISO: Resilience, risk, and the future of cybersecurity
This year’s Channel Islands Cyber Security Conference charged for tickets for the first time and still drew its highest turnout ...
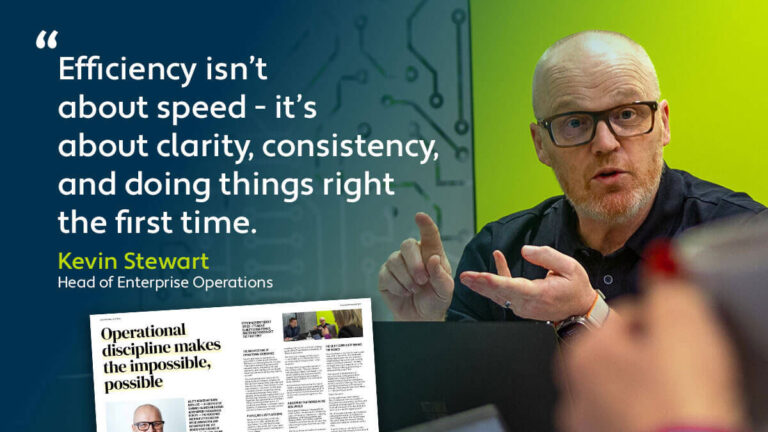
Operational discipline makes the impossible, possible
Operational excellence rarely makes the front page — but no matter what your business is, we all know it’s what ...

JT at MWC Barcelona 2025
Our teams were thrilled to be back at #MWC25 in Barcelona. Revisit our coverage ...
